Cloudflare Fixed Their Email Obfuscation Script (I May Have Caused It)
Cloudflare's email obfuscation script used to block rendering. A PM at Cloudflare read this article and shipped the fix. The SEO and security problems are still worth avoiding.

What is Cloudflare email obfuscation?
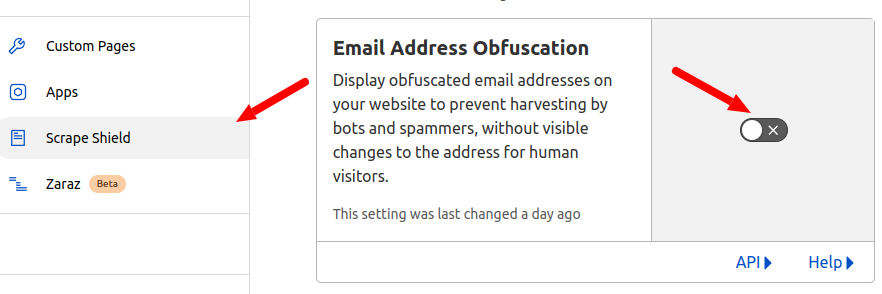
Cloudflare Email Address Obfuscation is a Scrape Shield feature that hides email addresses on your pages from email harvesters and bots, while keeping them visible to human visitors. It is enabled by default on every Cloudflare zone.
Last reviewed by Arjen Karel on April 2026
Table of Contents!
Update April 2026: Cloudflare fixex it. A Product Manager at Cloudflare messaged me on LinkedIn. He read this article and added the defer attribute to email-decode.min.js. Cloudflare's official documentation now confirms it: the script no longer blocks rendering.
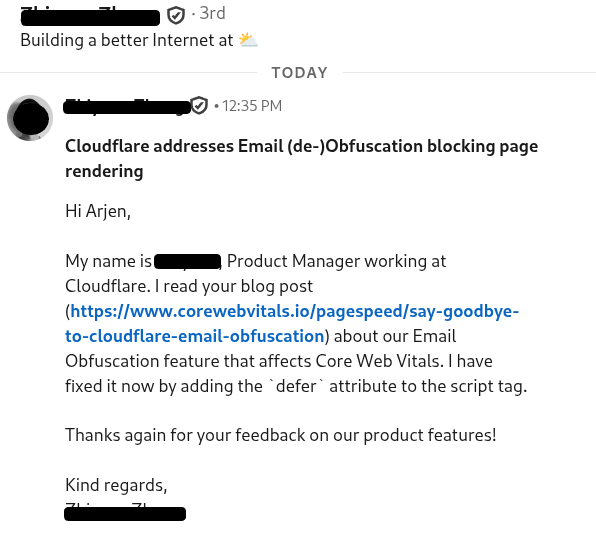
Defer is a one-line change. The reason it was not there in the first place was probably that Cloudflare wanted to confirm it would not break sites that depend on addresses being decoded before DOMContentLoaded. Someone on the team did the work. Credit where it is due.
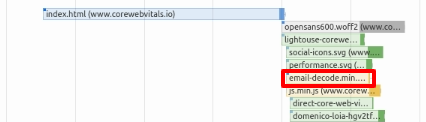
The way it works is simple. Cloudflare's edge proxy scans your HTML for anything that looks like an email address. It replaces each address with an XOR-encoded hex string and injects a small script called email-decode.min.js to decode the addresses in the browser. The script is about 1.2 KB, now loads with defer, and removes itself from the DOM after execution.
Until recently, that script was not loaded with async or defer. It blocked rendering. And it did this for a feature that most visitors will never notice or need. That is the situation this article originally described, and the reason Cloudflare fixed it.
 .
.
How Cloudflare email obfuscation used to affect the Core Web Vitals
 .
.
Before the defer fix, the email-decode.min.js script was injected as a render-blocking resource. The browser had to download, parse, and execute it before it could continue rendering the page. That had three consequences:
1. It competed for network bandwidth during the critical rendering window, delaying the Largest Contentful Paint.
2. It blocked the main thread, which could push the Interaction to Next Paint into "needs improvement" territory.
3. It triggered up to five Lighthouse audit warnings: eliminate render-blocking resources, avoid long main-thread tasks, reduce JavaScript execution time, avoid chaining critical requests, and serve static assets with an efficient cache policy.
With defer now in place, the script downloads in parallel with HTML parsing and runs after the document is parsed. The render-blocking warning is gone.
What is left after the fix
The main thread still has to parse and execute 1.2 KB of JavaScript. On a desktop that is nothing. On a low-end Android phone with a busy CPU, every small main-thread task chips away at your INP budget. If you are already fighting for the last 50 ms of INP headroom, this script is one more thing in the queue.
The bigger issues, the ones Cloudflare did not fix, are below.
SEO side effects
Cloudflare replaces email addresses with links that point to /cdn-cgi/l/email-protection#[hex]. These URLs return 404 to crawlers, including Googlebot. The result: "Soft 404" errors in Google Search Console. SEO audit tools like Ahrefs and Screaming Frog report them as broken internal links, creating noise that masks real crawl issues. If you use Cloudflare with email obfuscation enabled, check your Search Console coverage report for these phantom errors.
Is Cloudflare email obfuscation even secure?
Not really. Cloudflare uses a single-byte XOR cipher where the key is embedded in the encoded string itself. Every Cloudflare-protected site uses the same decoding mechanism. A spammer only needs to implement one decoder to extract email addresses from all of them.
Security researchers have demonstrated that the encoding is trivially reversible. Spencer Mortensen's 2026 obfuscation study tested 25 different methods against 300+ distinct spammers using honeypot email addresses. Even a simple CSS display:none technique achieved a 100% block rate against harvesters. You do not need a deferred JavaScript to hide an email address from bots.
Should you still disable it?
If you do not need email obfuscation (and most sites do not), turning it off removes the soft 404 crawl errors and the last few milliseconds of main-thread work. Here is how:
1. Log in to your Cloudflare dashboard.
2. Go to Security > Settings (or Scrape Shield on older dashboard layouts).
3. Toggle Email Address Obfuscation to OFF.
That is it. The script disappears immediately. For a full Cloudflare performance configuration, see the best Cloudflare configuration for passing the Core Web Vitals.
Disable per page with Configuration Rules
If you want email obfuscation on your contact page but not on high-traffic landing pages, use a Configuration Rule:
1. Go to Rules > Configuration Rules.
2. Create a new rule, name it (e.g. "Disable email obfuscation on landing pages").
3. Set the matching criteria (hostname, URL path, or both).
4. Add the Email Obfuscation setting and set it to Off.
5. Deploy.
You can also exempt individual email addresses in your HTML by wrapping them in comments: <!--email_off-->email@example.com<!--/email_off-->
If you need obfuscation: do it yourself
If you do want to hide email addresses from bots, there are much better ways that do not involve shipping any script before the user has expressed interest. The best approach: attach an IntersectionObserver and decode the email just-in-time when it scrolls into view. This is the same defer until needed pattern I use for everything from YouTube embeds to Google Maps.
Create the obfuscated email
<a class="email-hidden" href="#" data-email="aW5mb0BleGFtcGxlLmNvbQ=="> [email-hidden] </a>
Attach the IntersectionObserver. Place this piece of JavaScript at the bottom of the page.
<script>
const emailtag = document.querySelector('.email-hidden');
let observer = new IntersectionObserver((entries) => {
entries.map((entry) => {
if (entry.isIntersecting) {
let script = document.createElement('script');
script.onload = function () {
emaildecode(entry.target)
};
script.src = 'decode-email.js';
document.head.appendChild(script);
}
});
}).observe(emailtag);
</script>
Upload the email-decode script decode-email.js and replace the email decoding function with a decoding library of your own choice.
const emaildecode = (e) => {
let email = atob(e.dataset.email);
e.href = 'mailto:'+email;
e.innerHTML = email;
}
Check the results
<a href="mailto:info@example.com">info@example.com</a>
The email is decoded only when the visitor scrolls it into view. Zero impact on INP, no soft 404 errors for Googlebot, and the base64 encoding is no less secure than Cloudflare's XOR cipher. To verify the improvement with real visitors, set up Real User Monitoring. Lighthouse scores are useful for debugging, but field data from real users is what Google uses for ranking.
Search Console flagged your site?
I deliver a prioritized fix list backed by field data. Not a 50 page PDF.
Request audit